The latest Lifestyle Daily Life news tips opinion and advice from The Sydney Morning Herald covering life and relationships beauty fashion health wellbeing. For example the Hybrid Data Management community contains groups related to database products technologies and solutions such as Cognos Db2 LUW Db2 Zos NetezzaDB2.

Components Of M2m Communication Download Scientific Diagram
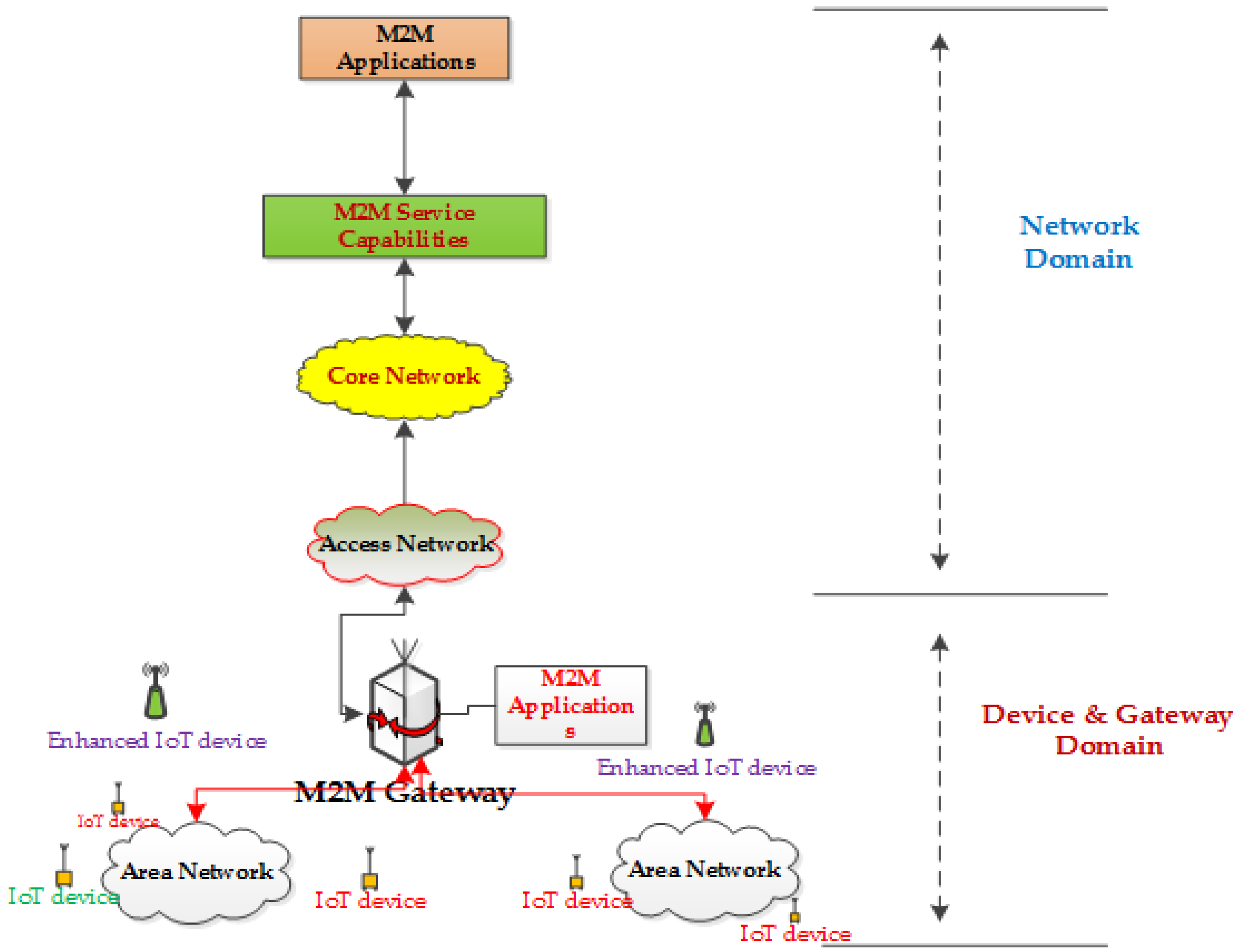
The IoTM2M devices need to remain connected despite they change their points of attachment frequently to the network either due to mobility or simply switching links in the overlapped wireless.

. If the process is not secure threat actors could intercept the update and install their own malicious update in which case they could have full control over the device and begin attacking other. Event featuring more than 150 exh. In 1973 he killed his mother and.
Most recently in three decades rapid growth was marked in the field of wireless communication concerning the transition of 1G to 4G 12The main motto behind this research was the requirements of high bandwidth and very low latency. Firmware replacement Updates and patches to devices are usually done remotely. First i made a sketch on paper and apply nailes on wooden plate.
American serial killer and rapist Ted Bundy was one of the most notorious criminals of the late 20th century known to have killed at least 20 women in the 1970s. 6 to 30 characters long. Must contain at least 4 different symbols.
Up to 4000 sq ft or small to mid-sized home with 65 dB gain. 5G provides a high data rate improved quality of service QoS low-latency high coverage high reliability and. ASCII characters only characters found on a standard US keyboard.
High Gain 10-12dBi Dual SMA Male 698-2700 MHz 3G4G LTE Omni-Directional Outdoor PoleWall Mount Antenna for Mobile Cell Phone Cellular 4G LTE Router Modem Gateway. But he soon stopped letting them go killing six young women in the Santa Cruz California area in the 1970s. Each solution concept or topic area has its own group.
More Best Practices RFID Journal LIVE. 2021 Report Part 2 RFID Journal recently hosted its 19th annual RFID Journal LIVE. He was executed in the electric.
Some of the most popular local exploits targeted by threat actors are as follows.

A High Level M2m System Architecture Download Scientific Diagram
A View Of A Machine To Machine M2m System Download Scientific Diagram
A General Architecture Of A M2m Application Download Scientific Diagram
Jsan Free Full Text A Cooperative Mac Protocol For A M2m Heterogeneous Area Network Html
0 Comments